Got a huge list of targets that you’d like to enumerate but can’t really visit each and every IP individually to see what service they might be running? Enters Eyewitness, it’s a tool written by Christopher Truncer written in Python which can scan a range of IP’s and URLs that then takes a screenshot of the service running on the default port (which is customizable) and saves them in a directory.
This can be greatly useful during a penetration test or while you’re bug hunting an organization with a vast scope. You might be able to gain a large range of subdomains through either Amass or Subfinder therefore it can make sense from a time saving perspective to automate the task.
Here’s how you can do it.
Installation
There are 2 ways through which you can obtain Eyewitness
- Automatic installation through APT
- Manual installation through Git
APT Method
Hop onto your terminal and type the following
sudo apt update && sudo apt upgrade -ysudo apt install eyewitness
Through GIT
The first thing we need to do is clone the Github repository, which can be done by the following command
git clone https://github.com/FortyNorthSecurity/EyeWitness This will clone all the files from the Git repository on your local machine.
The next step is to navigate into the setup directory inside the Eyewitness repository.
cd Eyewitness/setupNow that we’re inside the setup directory, simply running the setup.sh file will setup the environment for us and now Eyewitness.py can be successfully run without any errors.
Eyewitness Usage
Originally Eyewitness could only enumerate web services only but now it has support for RDP, Web, and VNC (Virtual Network Computing). You can either enumerate a single target or supply a list of targets. Eyewitness ties nicely with other recon tools such as Nmap, Amap, and Nessus as it can parse the XML, amap and .nessus files. Along with that just like many other Recon tools you can supply it with a text file as well.
eyewtiness --web --single https://example.comHere we’re specifying our target name as well as the method eyewitness should use. In case you’re unsure what service might me running on the target machine feel free to use the flag --all-protocols which will look for all the supported protocols mentioned above.
Once eyewitness gets to work you’ll be greeted with a prompt that’ll display the current progress as well as of a save screenshot confirmation.
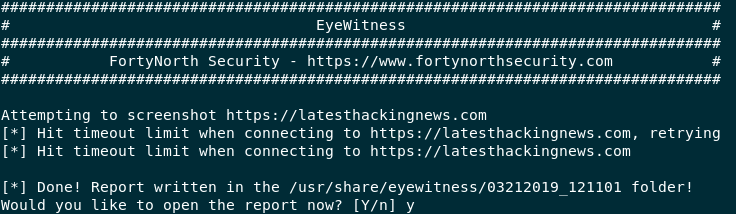
Eyewitness progress prompt and saving option
Note – If you receive a timeout, don’t fret, it’s possibly because of your internet connection. Try again.
Using Eyewitness for Multiple Targets
Using Eyewitness for a single target is neat but just for that purpose solely would be grossly under-utilizing the tool. To supply it with a list of targets here’s what you can you can do
eyewitness --all-protocols -f /root/targets/target.txtNote - Whenever you're supplying a list of targets make sure to supply a full path of the file instead of just the filename otherwise you'll be greeted with ERROR: You didn't give me a valid file name! I need a valid file containing URLs!
Once Eyewitness gets going you’ll see the same prompt but with a number of targets. Once you’ve saved the files you’ll be greeted with a new browser window with a list of all the targets all nicely setup in an auto generated web page.

Eyewitness output with an auto generated report.html file.
What Bunny Rating Does it Get?
Eyewitness is an essential tool in my arsenal for both bug hunting or enumerating a huge IP range on a penetration test and for better understanding of the services that are running. I would definitely recommend this tool for every large scope Bug Hunt, I am giving it 4/5 bunnies.




Eyewitness offers much more than just these options I highly implore you to dive into yourself. Feel free to leave a comment down below about your thoughts on the tool.
Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

