TheFatRat is an easy to use tool which helps in generating backdoors, system exploitation, post exploitation attacks, browser attacks, DLL files, FUD payloads against Linux, Mac OS X, Windows, and Android. It can be combined with msfvenom (Metasploit framework) which can be then utilized to utilise a reverse shell.
It offers a lot of features, but in this article, I backdoor with msfvenom.
Downloading and Installing TheFatRat
You can download it on Kali with the following command;
git clone https://github.com/Screetsec/TheFatRat.git

chmod 777 -R TheFatRat/
./setup

Running TheFatRat
Once the installation completes, start TheFatRat using;
./fatrat
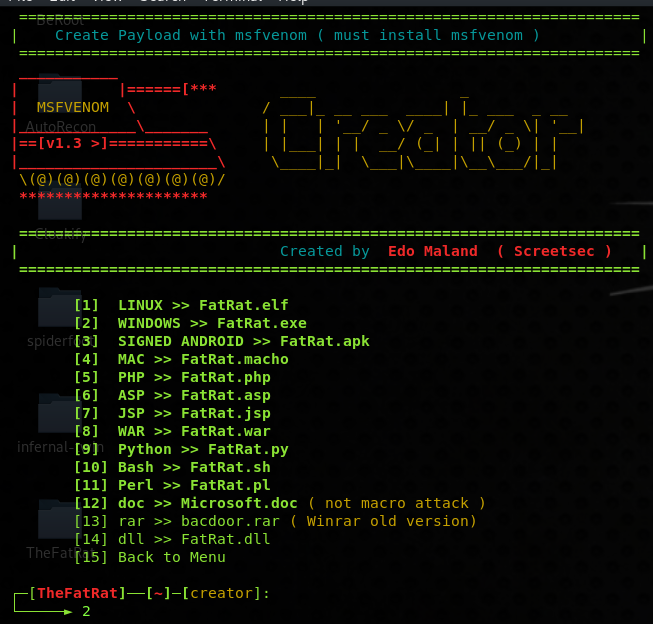
After it gets started, now to create the backdoor using msfvenom, use option 1.

Now select your preferred operating system or payload type, I am choosing a Windows one;
It will then ask you to set your IP address settings, name, and type of msfvenom payload, which you can set as per your requirement.

The exploit file will get created in the output directory of TheFatRat which you can then look into deploying on the test machine.

What Bunny rating does it get?




![]()
Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.


