According to the news in softpedia. The sample, dubbed HijackRAT, was analyzed by FireEye mobile security researchers, who found that the malicious APK poses as a Google Service Framework.
At the moment, it is aimed at stealing banking info from eight Korean banks, but the researchers say that the list can be further expanded in just half an hour of coding.
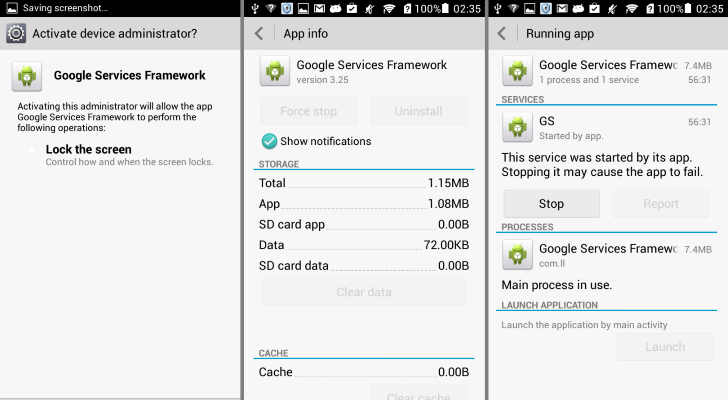
Once it is installed on the victim’s mobile device, the malwareplaces a new item on the home screen, under the name Google Services, marked with the default Android icon.
Upon launching it, the malware requests administrative privileges, which, given that it looks legitimate, most users would grant. This makes the process of removing it more difficult because not all users know how to strip an app of elevated privileges from Android’s Settings menu.
A process is then created, named GS, that communicates with the command and control server (C&C) for new instructions.
The researchers have identified the location of the C&C in Hong Kong, but it is unsure if it is under the direct control of the cybercriminals or it is another infected device used for sending the instruction set.
Attempting to relaunch the app generates an error saying “App isn’t installed,” and removes itself from the home screen, thus erasing any visible trace of its presence on the device.
The first malicious action taken by HijackRAT is to upload information about the phone (number and device ID) and the list of contacts available, possibly for duping other victims into infecting their devices.
FireEye says that HijackRAT targets a number of eight Korean banks, whose Android apps are replaced when the cybercriminal issues the update command.
The list of targeted banks provided by FireEye researchers appears to be the same, and both malware replace the legitimate banking app on the victim’s device through an update request.
CheetahMobile did not report the malware having any trouble replacing the official online banking apps.
In any case, if it is the same sample, FireEye gave it a name and published a more extensive analysis of the way it carries out the mischievous activity.