Researchers at the German security consultancy company, Curesec, found that the vulnerability can be exploited to terminate ongoing calls and to send short text messages to a specific number, although in this case user intervention is necessary.
Tthe flaw was introduced in version 4.1.x of the OS, which is also the most popular, with more than half (56.5%) of the Android users running it on their devices, according to statistics collected in the week up to July 7. Users of the KitKat version lower than 4.4.4 are also affected
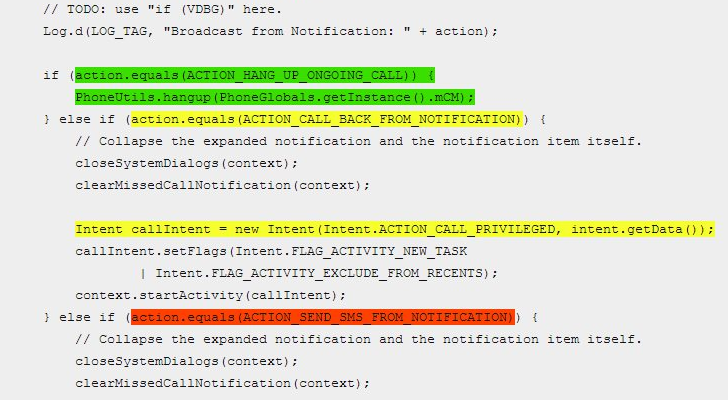
“However this bug is circumventing the situation and allows any malicious app to do a phone call, send mmi or ussd codes or hangup an ongoing call,” says the blog post from Curesec.
Furthermore, the researchers say that the bug can be exploited to run USSD (Unstructured Supplementary Service Data), SS (Supplementary Service) or MMI (Man-Machine Interface) codes, which can change various services on the phone, such as call forwarding, SIM card blocking, or turning on/off caller ID.
Unfortunately, there are no tools available for fixing the problem other than the latest update of android
“As the app does not have the permission but is abusing a bug, such apps cannot easily protect you from this without the knowledge that this bug exists in another class on the system,” say the researchers.
We suggest you not to download any app which does not having good ratings and bad reviews in order to avoid your mobile in vulnerable activity