Evilgrade is a modular framework that takes over target machines by injecting fake updates in poorly updated systems using a MITM attack strategy. Evilgrade has a WebServer and DSNServer modules to work as part of the MITM attack framework. Evilgrade requires the manipulation of the victim’s DNS traffic to operate. This can be achieved by any of the following methods.
– ARP Spoofing
– DNS Spoofing
– DHCP Spoofing
– TCP Hijacking
– Wifi AP Impersonation
– Having DNS access
Evilgrade is a modular framework. It is packed with a number of modules. Each module emulates a fake update for a specific application. The most commonly used applications include Notepad, Skype, Photoscape, Java 1.6.0_22 winxp/win7, VirtualBox (3.2.8 ), Filezilla, Ccleaner 2.30.1130, firmware, and Orbit.
Evilgrade Installation
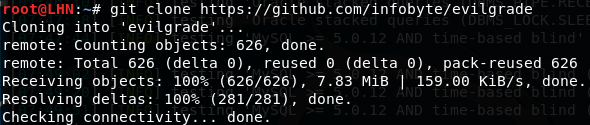
We can clone the Evilgrade repository from github using the following command.
git clone https://github.com/infobyte/evilgrade
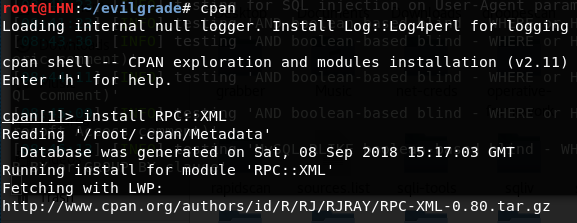
Evilgrade requires the following modules.
Data::Dump
Digest::MD5
Time::HiRes
RPC::XML
The required modules can be installed using the cpan shell. For example, type ‘cpan’ and then the following command to install the required RPC::XML module. Repeat the process for other modules by replacing the module name.
install RPC::XML
The alternate way of installing Evilgrade is by creating a directory and installing the Evilgrade in it. The directory can be installed as follows.
mkdir –p /root/evilgrade
Move to the newly created directory and install Evilgrade using the following commands.
cd evilgrade
tar -xvf isr-evilgrade-2.0.0.tar.gz
How to Run Evilgrade
After successful installation, run the Evilgrade framework using the following command in the terminal.
./evilgrade
The command will put Evilgrade into an interactive mode. To see the list of available modules, run the following command.
show modules

Currently, there are around 80 modules available in the framework. Select any module to configure and create fake updates. For instance, we can use the notepadplus module to create fake notepad+ application updates.
The module can be configured using the following command.
configure notepadplus
show options
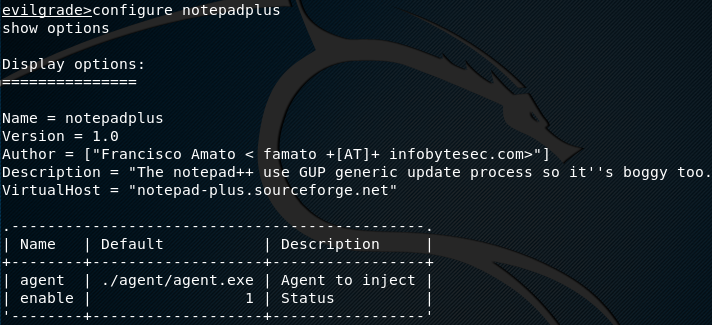
There are different options including the virtual host option. The virtual host option is used in the DNS setup for hijacking the updates. In the next step, we need to create a payload to be used as an agent in the fake update. The payload can be created using msfvenom or any other Linux tool. The reverse shell is used in the payload to connect with the target machine. Once the payload is created, it is passed to Evilgrade that runs it as agent using the following command.
set agent
Download the notepad+ setup as that is required during the interaction with the target host. After setting up the Evilgrade framework, the next step is to redirect the DNS traffic using any of the aforesaid methods. We also need to find out the available hosts to target. This can be achieved using any scanning tool. Once the target is identified, the next step is to send the payload to the target. The target gets a prompt message screen, showing them an available update for notepad+ application. If the user proceeds with the update, it is processed through the Evilgrade webserver. The agent from Evilgrade webserver moves to the victim’s machine. Since it is equipped with the reverse shell, a shell is created on the victim’s machine to exploit the target host.
What Bunny rating does it get?
Evilgrade is a powerful framework, equipped with a number of modules that can generate fake updates very cleverly to inject in the target hosts. However, the Evilgrade role is secondary. First, one must have to manipulate the dns traffic to make the tool work. Another drawback of the tool is its limitation of working with only application/software that does not require digital certificates for authenticating the requests. As a result we will be awarding this tool a rating of 3.5 out of 5 bunnies.



![]()
Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

